End-to-End Encryption for Twilio
In this guide you will learn about adding end-to-end encryption to your product to secure your messages and user data that you deliver using Twilio Programmable Chat.
Benefits of E3Kit for Twilio
- Full privacy: Only user can read their own messages; Twilio, Virgil and other third-party services cannot decrypt and access messages and data.
- Complete end-to-end encryption: User's data is always encrypted and protected - at rest and in transit.
- Independent data protection: With E3Kit your data protection doesn't rely on any network and service providers, so any attacks on them won't influence the data integrity and confidentiality.
- Data integrity: The E3Kit signs and verifies data as part of the encrypt and decrypt functions. This confirms that data is actually coming from the user who encrypted it and that it hasn't been tampered with in transit or storage.
How end-to-end encryption works with Twilio
End-to-end encryption consists of securing data between two users or endpoints using a private & public key for each user or endpoint:
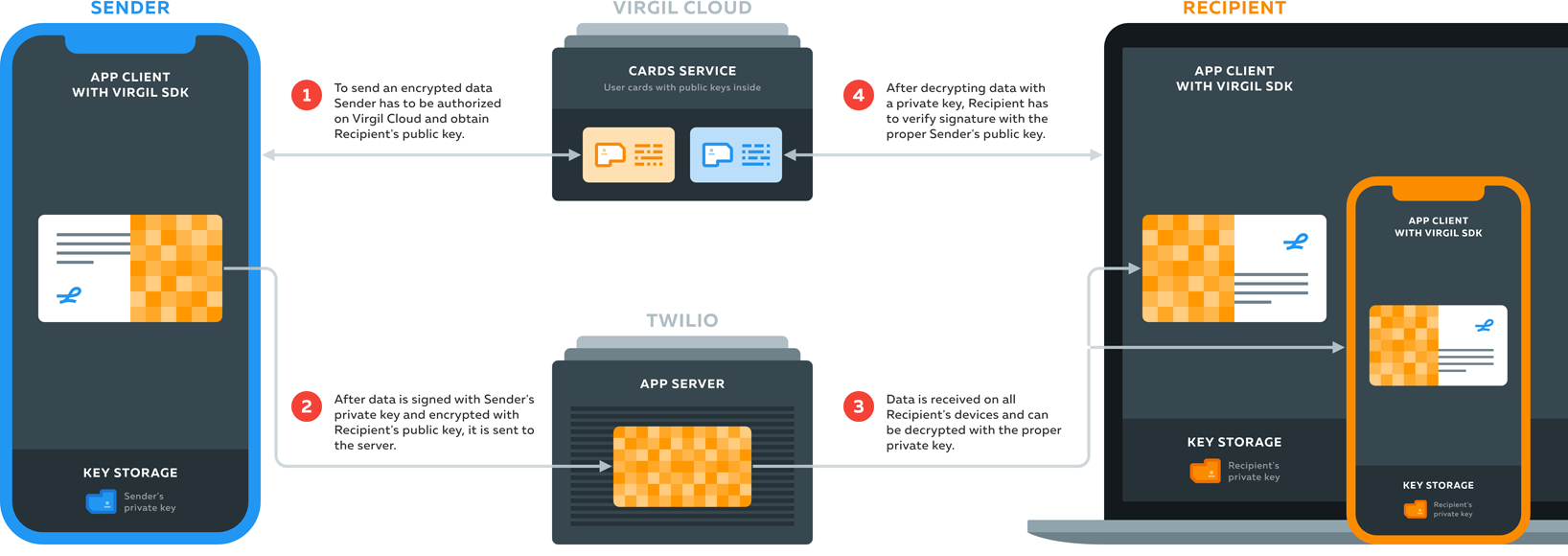
- Twilio SDK on the Client side allows users to send and receive messages, join groups and communicate with Twilio backend in other ways, while Virgil handles encryption of users' messages and data.
- Virgil E3Kit on the Client side allows you to generate a public and a private key for your user.
- The public key is published to Virgil Cards Service, part of the Virgil Cloud PKI. When your users want to send a message, the Virgil E3Kit uses the recipient's public key to encrypt the message data in a way that only the recipient's corresponding private key can decrypt it.
- The private key is kept on the end-user's device, enabling the user and only the user to decrypt any messages or data that other users sent to them. It's similar to the relationship between a public mailing address and a private mailbox. You look up someone's address to send them a letter, but only they can unlock their mailbox to open and read the letter.
The address book (Virgil's Cards Service), mailing address (public key) and mailbox key (private key) are related to each other, but can't be traced to each other in any way that would compromise the security of the system. End-to-end encryption also locks the letter (message data), and only the recipient has the key to unlock it.
This setup enables users to encrypt a message on their phone or computer, send it over the Internet with the help of Twilio to a recipient without any chance of another party reading it in transit or on the server, and have it be decrypted only by the recipient on their phone or computer. This all works seamlessly for the end-users and it only takes a few lines of code to implement using E3Kit.
Get started
Step 1: Twilio Programmable Chat
You must have a working Twilio project with a channel set up to send and receive messages. If you don't, please follow Twilio's documentation.
Step 2: Backend for Twilio and Virgil JWT generation
In order to be able to encrypt/decrypt messages and use a Twilio Programmable Chat, your users have to be authenticated using JWT at Virgil and Twilio services. So, you need a backend code that generates Virgil and Twilio JWTs with the help of Virgil Core SDK and Twilio Helper on your Server side.
For this tutorial we've created a sample backend code that demonstrates how to combine Virgil and Twilio JWT generation. To setup and run the sample backend locally, head over to Twilio-Sample-Backend-NodeJS GitHub repo and follow the instructions in README. You can easily use it as an example to build own backend for a JWT generation.
Step 3: Virgil's end-to-end encryption
Once you have a working Twilio channel and backend ready, you can follow our Get Started to set up E3Kit on client side in order to encrypt messages before you send them to Twilio and decrypt the messages after you receive them.